
Enrich Sentinel with real-time reconnaissance & exploitation intelligence.
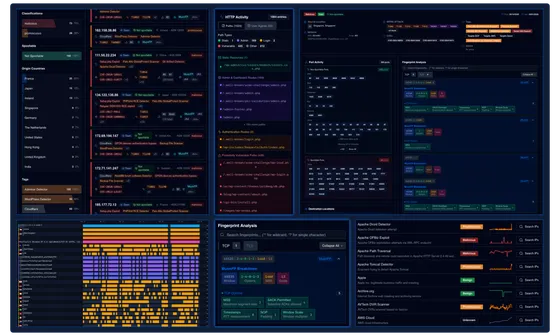
Add real-time threat intelligence across Microsoft Sentinel - from Analytics Rules and Incidents to Entities and SOAR workflows - to improve detection quality, prioritization, and response.
Built for Microsoft Sentinel workflows.

Increase detection confidence in KQL Rules
Improve signal quality in Analytics Rules by enriching detections with real attacker and exploitation context.
Prioritize real threats over alert noise
Enrich Sentinel Incidents with mass exploitation and reconnaissance intelligence so analysts can triage faster and escalate accurately.
Speed up entity investigation decisions
Enable faster analyst decisions by turning Sentinel entities into enriched, behavior-aware threat signals.
Automate response with higher trust
Feed Logic Apps playbooks with real-time threat context to automate blocking, suppression, escalation, and response actions.
Separate what needs action from what doesn’t.
Enrich Sentinel signals with threat intelligence and behavioral context to distinguish real threats from benign activity.
High-risk exploitation traffic
IP connections linked to active mass exploitation campaigns targeting vulnerable services.
Reconnaissance & vulnerability scanning activity
Promiscuous internet scanners probing exposed assets for known weaknesses.
Suspicious authentication behavior
Login attempts originating from infrastructure associated with active reconnaissance and exploitation activity.
Financial fraud indicators
Transactions correlated with known malicious infrastructure or high-risk behavioral patterns.
Remote code execution attempts
Activity associated with exploit attempts targeting application or system-level vulnerabilities.
Botnet-driven activity
Traffic originating from opportunistic botnets used for scanning, exploitation, or secondary payload delivery.
Automated credential spraying campaigns
Large-scale “spray-and-pray” authentication attempts across multiple targets.
MITRE ATT&CK mapping context
Enrichment of security events with MITRE ATT&CK techniques and adversary behavior mapping.
Yes. Your environment is constantly scanned.
No. You don’t need every scan in your incident queue.
Reduce Sentinel noise by filtering out constant scanning activity, AI/ML scraping tools, and benign research crawlers.
Strengthen the perimeter for cleaner Sentinel signals.
Integrate ELLIO Threat Intelligence as a pre-SIEM filtering layer (IP Blocking) in Azure Firewall to improve perimeter protection and reduce unnecessary noise before it reaches Microsoft Sentinel.
![[watchdog]: Inside a Mirai variant with six-layer persistence](/_astro/Mirai%20Botnet%20with%206%20layers%20of%20persistence%20Hero_Z2qvA8g.webp)

